In the past few months, we heard over and over how big corporations such as Sony and Anthem have been hacked and customer information stolen. It’s not just information for one or two folks but thousands, even millions. And you know what? This happened regardless of what YOUR personal password was! In fact, what I’m going to suggest is that whenever someone with whom you have an account asks to keep changing your password “for security reasons,” you should change it to “Bullshit!”
Hackers are not interested in my password for the Speech Dudes site. They really are not. Any hackers who are going to spend hours and hours trying to break into this account so as to upload a picture of a skull-and-crossbones and say “Yah boo sucks, Dudes, you’ve been hacked” are one card short of a deck; two fries short of a Happy Meal; three sandwiches short of a picnic. Their lights are on but no-one’s home; their elevator doesn’t go to the top floor; and their cheese has slid so far off the cracker that their collective intelligence can only be matched by that of a shed-load of broken garden tools.
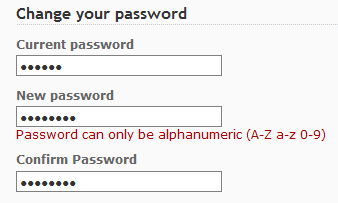
Just last week I wanted to check my recent health insurance bills from United Medical Resources (UMR) only to find that before I could, I have to change my password “for security reasons.” Fair enough – except that this is the third time in a year I’ve had to do it. And what’s more, I can’t use ANY of the past 10 passwords I’ve used, which means I have to invent new ones every time.
This “you cannot use any of your previous 10 passwords” is also an irritation because it (a) forces me to create yet more mindless character strings than I need to remember and (b) tells me that the Grand Keeper of the Passwords at UMR has a list of all my previous ones. “Someone” is tracking my passwords! And if “they” are keeping my passwords, and “they” are hacked, I’ve not just lost my current password to hackers but all my previous ones – which may in turn include ones that I am still using for other accounts.
Some sites have now introduced not just the password but some stupid picture that is supposed to help; by making you now remember both a password AND a picture! And hey, hey, hey, it’s not just pictures: my friend Kara has an account where they also include what they call a “personal security phrase,” which in her case was “devoted corn.” Devoted Corn! I’d love to stuff that devoted corn down the throat of the person who came up with that idea!!! So now she has to remember her password, “devoted corn,” and her “personal image.”
All I can take from this madness is that I bet the sale and use of sticky notes has gone up significantly over the past five years because let’s get real and acknowledge what people actually do with regard to passwords:
They make a list.
Sure, you might have a list that you store in an encrypted format using a piece of software (presumably written by the folks who have developed these password/image/personal-phrase systems) but you’re still making a list. And when folks like UMR and Apple stop you using previous passwords, you can’t even have the option to have just one “open sesame” for all your accounts. Apparently that’s a bad thing. But that didn’t help all the folks who had accounts in 2014 with Sony, Target, Anthem, Neiman Marcus, AT&T, eBay, PF Chang’s…
It’s the hacking of all those big, international corporations that points to where the real danger lies. It’s not from some guy in Russia [1] trying to get MY personal password for Chase Bank, but from some guy in Russia trying to get ALL the passwords for Chase Bank at a corporate level. The personal password might make me feel safe but the evidence is that I’m no safer having the word “password” for all my accounts than someone who has “XX345Xbbg$3iOO” and anagrams thereof for every single account they use. During my recent trip the ATIA 2015 conference at the Caribe Royale Hotel in Orlando, Florida, myself and a number of other colleagues had their credit card numbers stolen, with all evidence pointing to someone having access to the desk at the on site Cafe (the only place where we all used a card). No passwords were involved, just the opportunity for someone to see numbers in a hotel system [2], and opportunist theft is something that can happen to anyone.
The danger I face from having “Captain Danger” as my one and only password for all my accounts is not that some hacker will work it out. The danger is from having an account in the first place with a company whose security system is lacking. If they employ highly paid so-called “security experts” whose answer to breaches is to tell all their customers to change their passwords, I suggest they recognize them for what they are – Naked Emperors. Get them to do their job and make the system secure or sack ’em and employ some East European hacker to bolster up your website and pay them with a subscription to XBox live for a year and a free download of Grand Theft Auto 6 – although there’s a good chance they’ll hack a pre-release freebie long before the product is released to paying customers.
 I want three, maybe four, passwords for all my accounts. I want them to last forever. I want to be allowed (yes, it’s my choice, after all) to use whatever characters I want no matter how simple, stupid, or “obvious” some over-hyped security expert thinks it is. And I want my health insurance company (to whom I give lots of cash), my bank (to whom I give lots of cash), and my wireless phone company (to whom I give ever-increasing amounts of cash), to get their acts together and stop trying to blame me for being unable to handle passwords when they seem unable to protect their own systems.
I want three, maybe four, passwords for all my accounts. I want them to last forever. I want to be allowed (yes, it’s my choice, after all) to use whatever characters I want no matter how simple, stupid, or “obvious” some over-hyped security expert thinks it is. And I want my health insurance company (to whom I give lots of cash), my bank (to whom I give lots of cash), and my wireless phone company (to whom I give ever-increasing amounts of cash), to get their acts together and stop trying to blame me for being unable to handle passwords when they seem unable to protect their own systems.
Rant over. Let the flames begin!
Notes
[1] Before any Russian readers decide to hire a hacker to crash this blog because they think I’m being unkind to them, I use the example of Russian hackers because according to a 2013 article from the Gartner Group, it is “fairly well-known by most security professionals that the best hackers on the planet often originate from Russia.” Deutsche Telekom has a fascinating little site that tracks real-time hacks across the world (http://www.sicherheitstacho.eu) and during January 2015, China took first place by a wide margin, with the US taking silver, and Russia slipping down to a mere bronze. Another fascinating “live attack” site comes from the company Norse, and if they were to create a live wallpaper based on their http://map.ipviking.com map, I’d be using it!
[2] I’d be curious to hear if any other fellow attendees experienced card theft. I wrote to the hotel to alert them to the multiple thefts but heard nothing back – which may be expected because no-one wants to admit to having lax security.





Here’s a great video from singer, Christine Lavin, called “The Password Song.” Well worth a listen 😉
Alright Dudes, I love you guys and there’s nobody I’d trust more on Speech and Linguistics. But there’s lots wrong with this post!
Before I trash it, let me say I agree with the core premise: identity management is a huge cluster, and placing more onus on the end-user is a big problem.
However, you’ve got a core fact wrong, and it really leads to lots of statements (made with authority – kudos) that are quite false. That core fact is this: 90%+ of the sites you log into never actually store your password. And 0% of those with a “list of your past 10” store them at all.
Let me explain. Web sites (like ours & every other one that matters) don’t store the password, they store a “one-way hash” of the password. I know this is a little technical, but hear me out: it matters.
In vary layman’s terms, one-way hashes take a piece of text (your password) and run an algorithm to “scramble” it. That algorithm can’t be undone. So you can never take the result of the scramble (the “hash”) and get back your password. BUT, if you use the same one-time hash again on your password, you’ll get the same scrambled version.
Here’s a walk-through of a very insecure one-way hash. Our algorithm will simply lookup the order of each letter in the alphabet and add that to a running sum. We’ll use the password ‘sesame’.
S 19
E 5
S 19
A 1
M 13
E 5
—————
Total: 62
So, if you give me the password and I get the “hash” of 62, I will store that for later. If you later give me a password and I calculate the hash of 62, I can be pretty sure it’s the same one you gave me last time.
Modern one-way hashes are much more secure than that silly example. Most sites use one called “md5” although others like ‘SHA1’ are probably more secure. For reference, the md5 of ‘sesame’ is ‘b3fba6554a22fdc16c8e28b173085ccc’. And there is zero chance I could go backwards from that to ‘sesame’.
So, that means that those pesky sites aren’t letting your password lie around. And the ones with lists aren’t either: they have a list of your past 10 hashes and they check your password against all of them. They are irritating, but there isn’t a risk of others learning your password from what they store (reading it on the wire is another matter).
Now: why do they make you go through the “tough password” game? Well, lets say that someone actually did break into the site and get a list of all of those hashes? What could they do with them? You can’t go from the hash to the password… but you CAN test words against them! Welcome to the world of the “dictionary attack”. This is where jerks take every word in English and check it against the list of hashes! Then they try common non-word passwords (“P@$$WORD”, “password123”, “abcd1234’, etc.). They can check each one against every entry in the list and eventually they will find someone with a dumb password like ‘sesame’. And hence you have a breach. And computers are VERY good at running through massive dictionary attacks very quickly.
What are we to do? Well – choose good passwords. Non-trivial ones that are easy to remember. Pick a song lyric and take the first letter from each word with a number and special character thrown in (see if you can guess “AlAaTlP&”) . Or, if you’re a touch typist, make it your normal password with your hands shifted up one row (‘sesame’ -> ‘w3wqj3’). Find a phonetic password generator and keep playing until you find one that’s catch – I used one for years. http://tools.arantius.com/password
Finally, know which things to stress about. For example:
They want long passwords that aren’t words – GOOD
They want you to change it fairly often – OK: it protects you from certain attacks
They don’t let you repeat passwords – FINE: it doesn’t help or hurt
They don’t let you use SIMILAR passwords – RUN AWAY! Remember, hashes shouldn’t let them know about similarity, so this means they are storing your password
They send password reset links by email – SO SO: it implies email is safe which it isn’t, but it’s pretty common.
They send PASSWORDS by email – NOPE: again, they shouldn’t store your password.
If you want to learn more, I recommend Bruce Schneier’s Applied Cryptography – a GREAT book that is very easy reading (for the first few chapters) and that will open your eyes. Or, take a computer security class from MIT (Open Courseware).
Anyhoo – I hope you had a great weekend, and I look forward to your next Speech Rant 🙂
Bill
Thanks for the detailed explanation of how hashing works and how to choose a good password – that’s useful for folks to take to heart and given that we’re all stuck with passwords, then having one that’s closer to the “impenetrable” end of the scale than “this really isn’t a password” end. And it’s good to know that 90% of the time passwords are not being stored. I guess my beef is, and you did, of course, highlight that right up front, with the user experience and the seeming over-reliance on me (and others) having to take on the cognitive load. And as the user, knowing my passwords are not just sitting there as snippets of text might offer some comfort, but the experience of having to change a password three times in a year, or being unable to use any of my previous 9 passwords is still existentially a pain. Studies have shown over and over that folks choose “easy” passwords not because they are stupid but they are human and their memories are fallible. The folks at Consumer Reports took a survey in 2012 where they said that over 50% of folks have more than 6 password-protected accounts online, that 32% use a personal reference in their password, that 20% use the same password for up to five of their accounts, and almost 25% keep physical lists to remind them. And in an article in ComputerWorld (which was one of a few that prompted the rant), the author writes that “Passwords have been dead for years. Security experts have been advocating the need for companies to raise the bar on user authentication for a long time.”
So my irritation at the level of consumer, not programmer. If there were a way for me to have one password and a second method of authentication method I could use across accounts, that would be splendid. However, that’s in the hands of developers, and I’m sure folks are working on this (bio-metrics, etc.) I’ve had the same pin code for ATM access for 30 years and so far that’s worked out fine. Of course, there’s an inherent 2-factor element; card plus pin, and probably some clever behind-the-scenes monitoring to check I don’t draw out $200 fifteen times in an hour.
I’ve added you suggested reading to my Amazon wish list. I’d also suggest, if I dare, that you might a stand-alone blog post on passwords and password security, above and beyond what you mention above. Passwords may be “dying,” as some articles suggest, but until their eventual demise, any specific advice on how best to balance security with “dear Lord not another password!” would be brilliant. Maybe even a guest blog (something we’ve not done yet but always had on the books)?
Keep on reading, and keep us on our toes!
The “stupid picture” is there to protect you from copycat “phishing” sites. It is supposed to authenticate the site to you, not you to the site.
Thanks for that reminder, Mark! Yes, sometimes part of the process is to provide that “quick check” that you’re at the right site and not amazoon.com, where an extra letter can mean the difference between your booked being delivered or you ass being handed to you! As I mentioned in the LessonPix reply, I’m focusing on my reactions as a user, where I am faced with having to retain different pieces of information, and the picture is an example of one more piece of data I have to attend to. It may well be that a picture seems easier to recognize than a password is recalled but it still represents a “data chunk” that gets added to my (or any user’s) load. I understand that it offers extras security but as the number of different passwords, pictures, and personal security phrases increases, so does the difficulty to remember them. Hence many folks keep lists of passwords, or use the same ones over and over. But thanks for reminded us – and our readers – that security can take more forms than just a password.